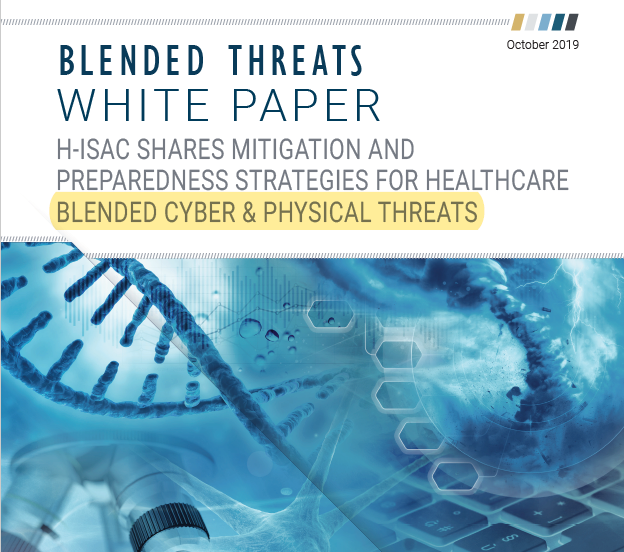
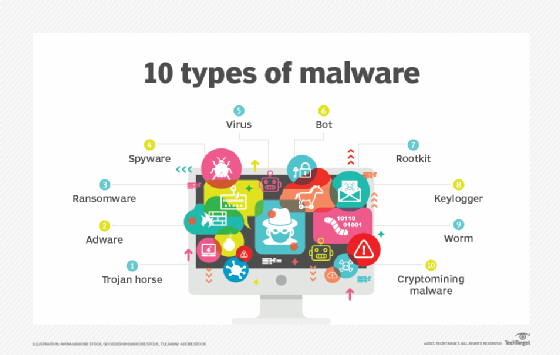
Whiz Security - Blended Threat A blended threat is an exploit that combines elements of multiple types of malware and usually employs multiple attack vectors to increase the severity of damage and

Internet Blended Threat Stock Photo - Download Image Now - 2015, Aggression, Antivirus Software - iStock

Computer Worm Computer Virus Trojan Horse Malware, PNG, 500x559px, Computer Worm, Artwork, Blended Threat, Computer, Computer

Blended Threat - Inscription on Blue Keyboard Key Stock Image - Image of network, service: 177568647


![4. Blended Threats: When Applications Exploit Each Other - Hacking: The Next Generation [Book] 4. Blended Threats: When Applications Exploit Each Other - Hacking: The Next Generation [Book]](https://www.oreilly.com/library/view/hacking-the-next/9780596806309/httpatomoreillycomsourceoreillyimages321278.png)